Learning cybersecurity is no longer a luxury in an age where data is the real wealth, and protecting digital systems has become a necessity to protect individuals
With the acceleration of digital transformation in Saudi Arabia and the UAE, and its association with Vision 2030 and smart initiatives.
There is a need for qualified personnel and a strong cyber infrastructure that supports a knowledge-based economy.
The Scientific Club Academy offers a complete guide and a professional training course that helps you understand the basics of cybersecurity.
Start your journey now to secure your future, gain the required skills, and launch into the labor market with confidence, especially in the Saudi and UAE markets.
and build a career in one of the most in-demand fields.
What is Cybersecurity? Learn Cybersecurity
Cybersecurity The set of technologies, processes, and controls designed to protect systems, networks, programs, and data
From digital attacks, damage, or unauthorized access, it's about maintaining the confidentiality, integrity, and availability of information in cyberspace.
Basic Principles of Cybersecurity: The CIA Trilogy
- Confidentiality: It means ensuring that information can only be accessed by authorized individuals, this prevents disclosure
Examples of confidentiality mechanisms include encryption, strong passwords, and access control.
- Integrity: Ensure that the information is accurate, complete and not modified by unauthorized parties, the goal is to prevent data manipulation.
Integrity can be achieved through hashing, digital signatures, and error-checking mechanisms.
- Availability: Ensure that systems and data are available to authorized users when they are needed. This means protecting systems from attacks aimed at disrupting services, such as distributed denial of service (DDoS) attacks. Availability mechanisms include data backup.
Disaster recovery plans and fault-tolerant systems.
Common Cyber Threats
- Malware: An umbrella term that includes viruses, worms, Trojans, ransomware, and
Spyware, which aims to damage systems or steal data.
- as well as phishing: Attempts to trick individuals into revealing sensitive information (such as usernames and passwords)
by masquerading as a trusted entity in an electronic communication.
- Distributed Denial of Service (DDoS) attacks: Flooding a system or network with a flood of fake traffic to prevent legitimate users from accessing services.
- Social Engineering attacks: The psychological manipulation of people to make them perform certain actions or reveal confidential information.
- Zero-day Exploits: Exploit vulnerabilities that are not known to developers or the public, making them difficult to detect and protect against.
Why learn cybersecurity now?
There is unprecedented demand for specialists in this field, driven by rapid digital growth and the increasing complexity of cyber threats.
Here are some key reasons why learning cybersecurity is a strategic choice:
1. High demand for jobs and a shortage of talent
In the MENA region, specifically in Saudi Arabia and the UAE, this shortage is growing exponentially as the pace of digital transformation accelerates.
This means that qualified individuals in cybersecurity have abundant career opportunities and a guaranteed career future.
2. Rewarding salaries and a progressive career path
The career path in this field offers opportunities for continuous growth and development.
From entry-level cybersecurity analyst to security engineer, then security consultant, all the way to leadership positions such as Chief Information Security Officer (CISO).
3. A dynamic and constantly evolving field
This field is exciting and stimulating, as it requires professionals to be constantly learning and adapting, if you are looking for a career that is characterized by novelty and intellectual challenge.
Cybersecurity is the best option.
4. Contribute to the protection of society and the economy
Protecting personal data, stabilizing critical infrastructure, and ensuring business continuity is a career that gives you a deep sense of purpose
and contribute positively to society.
5. Work flexibility and global opportunities
It is in demand everywhere, opening doors to international career opportunities and the possibility of working with leading global companies.

Cybersecurity in Saudi Arabia: Vision 2030 and Digital Transformation
The vision aims to build a thriving economy, a vibrant society, and an ambitious nation, all of which rely heavily on a secure and reliable digital infrastructure:
National Cybersecurity Authority (NCA)
Established by royal decree in 2017, KDIPA's main tasks are to:
- Policy and strategy development: Developing national cybersecurity policies and strategies to ensure the protection of the Kingdom's cyberspace.
- In addition to building national capacities: Work to develop and qualify national competencies in the field of cybersecurity through educational and training programs.
- As well as promoting awareness: Raising awareness of cybersecurity among individuals and organizations.
- Incident Response: Coordinate to effectively respond to cyber incidents and protect critical infrastructure.
- International cooperation: Promote cooperation with international organizations and other countries in the field of cybersecurity.
and the evolution of the industry.
The Role of Cybersecurity in Vision 2030
- Prosperous economy: Protecting businesses and organizations from cyberattacks ensures business continuity and boosts confidence in the digital economy.
This attracts investment and supports the growth of new sectors.
- Also, a vibrant community: Protecting the personal data of citizens and residents and securing digital government services enhances confidence in e-transactions
It contributes to building a safe digital society.
- As well as an ambitious nation: Securing the country's critical infrastructure (e.g. energy, water, telecommunications) against cyberattacks is critical to maintaining
on national security and stability.
Career opportunities in cybersecurity in Saudi Arabia are growing exponentially, with government and private companies looking for qualified specialists
To protect its systems and data, this makes the Kingdom an ideal destination for those wishing to build a successful career in this field.
Cybersecurity in the UAE Innovation and Smart Cities
Cybersecurity is increasingly emphasized as an essential element to ensure sustained innovation and the protection of digital assets:
UAE Cybersecurity Strategy
This strategy focuses on several key areas:
- Enhancing Cyber Resilience: Build strong capabilities to quickly respond to and recover from cyber threats.
- As well as developing competencies: Invest in the education and training of national cadres in the field of cybersecurity.
- Innovation, research and development: Support innovation in cybersecurity technologies and the development of localized solutions.
- In addition to international partnerships: Strengthening cooperation with countries and international organizations to counter cross-border cyber threats.
- As well as data protection: Establish strong legal and regulatory frameworks to protect personal and organizational data.
Smart Dubai and Cybersecurity
Smart Dubai is a prime example of how cybersecurity can be integrated into the core of digital transformation initiatives, with Dubai aiming to be
The smartest and happiest city in the world, this requires strong protection of data and systems that support smart services, such as smart transportation.
The Digital Dubai Authority is working to implement cybersecurity strategies for smart healthcare and digital government services.
advanced to ensure the security of these initiatives.
This creates a constant demand for professionals who are able to secure these new technologies, making the UAE an attractive center for professionals
Aspiring cybersecurity professionals.
Key Areas of Cybersecurity
1. Network Security
This includes securing wired and wireless networks, firewalls, intrusion detection and prevention systems (IDS/IPS).
and virtual private networks (VPNs), network security engineers are responsible for designing, implementing, and maintaining network security solutions.
2. Application Security
(From Source Code Analysis, Penetration Testing of applications, and Secure Development Life Cycle (SDLC) practices, application security developers and testers ensure that software is secure from design to deployment.
3. Data Security
Identity and Access Management (IAM), data protection policies, backup and recovery.
Data security professionals ensure the confidentiality, integrity, and availability of information.
4. Cloud Security
Focused on protecting data, applications, and infrastructure hosted in cloud environments, this area requires an in-depth understanding of liability models
Shared Responsibility Model between the service provider and the user, securing cloud configurations.
5. Endpoint Security
This includes anti-virus and anti-malware software, vulnerability management systems, and hard disk encryption.
Endpoint security specialists ensure that every device in the network is adequately protected.
6. Incident Response & Digital Forensics
To recover affected systems, this requires strong analytical skills and a deep understanding of digital forensic tools and techniques to collect and preserve evidence.
7. Risk Management & Compliance
(e.g. GDPR, ISO 27001, PCI DSS), our risk management and compliance consultants help organizations build robust security programs that comply
with legal and regulatory requirements. Each of these fields offers a specialized career path, and those interested in cybersecurity can choose to specialize
that matches their passions and skills.
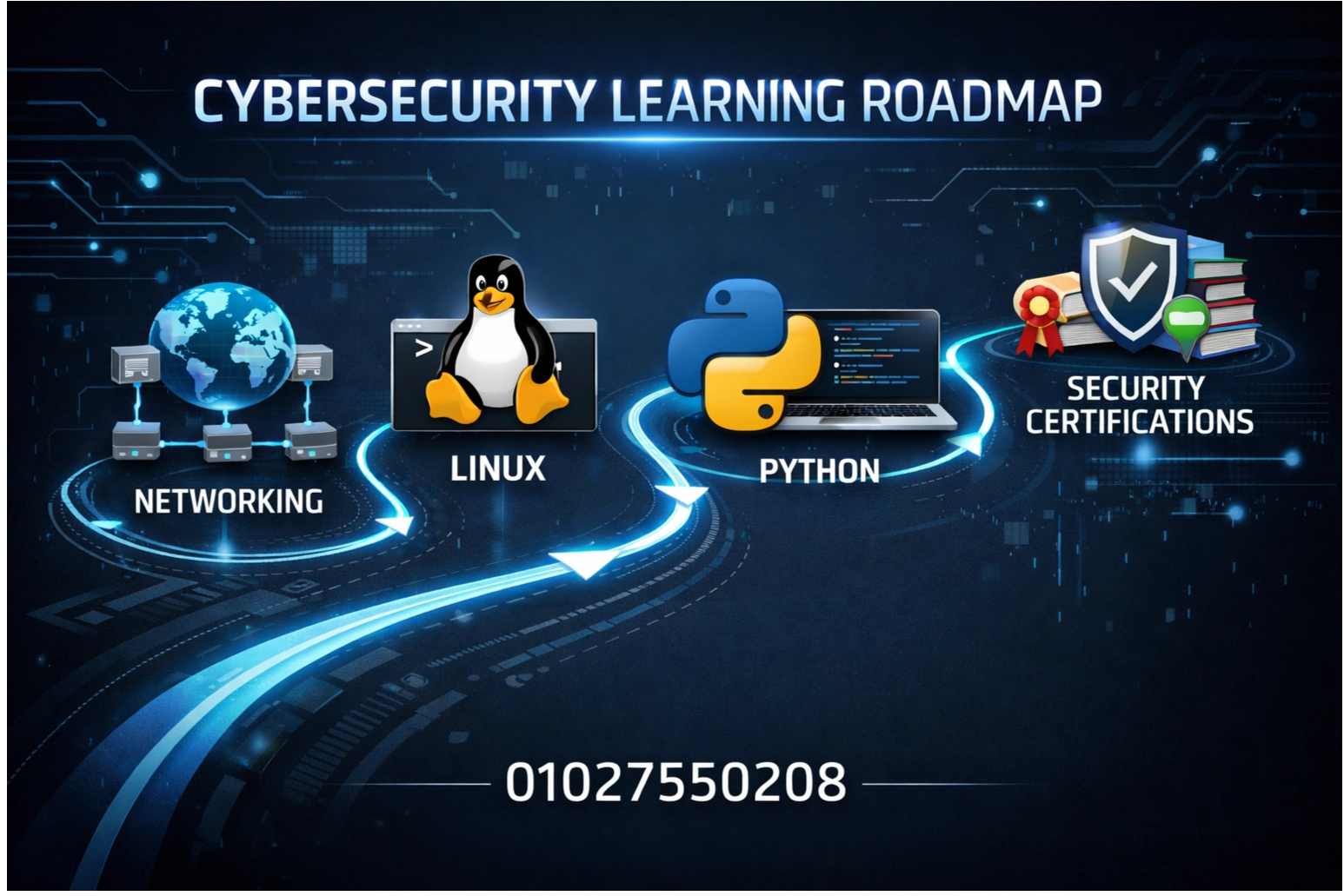
Your cybersecurity learning journey for beginners
You can build a strong foundation and launch a successful career, here are the basic steps:
1. Building a strong technical foundation
- Operating Systems: Understanding how operating systems such as Linux and Windows work, file management, and permissions.
and operations, Linux is particularly important in cybersecurity.
- Networking: Understanding the basics of networking, such as TCP/IP protocols, IP addresses, and concepts such as firewalls.
Routers, switches, and certifications such as CompTIA Network+ can be an excellent starting point.
- Also, Programming: Learning at least one programming language, such as Python, will give you a huge advantage. Python is widely used in cybersecurity to automate tasks, write tools, and analyze data.
- Databases: Understand the basics of databases and how to interact with them, as many cyberattacks target databases.
2. Understand basic cybersecurity concepts
For identity and access management, you can start with introductory courses or certifications like CompTIA Security+, which cover a wide range of these concepts.
3. Choosing a field of specialization
4. Hands-on learning and application
- Virtual Labs: Create virtual environments (using VMware or VirtualBox) to experiment with security tools and technologies
without risking your real systems.
- There are also challenge platforms (CTF - Capture The Flag): Participate in CTF challenges that provide real-life security scenarios to solve, helping you
to develop your skills in penetration testing and forensic investigation.
- As well as personal projects: Build small security projects, such as setting up a firewall, or writing a Python script to automate a security task.
or analyze network traffic.
5. Obtaining professional certifications
are globally recognized, and we will review some of the most important ones in the next section.
6. Networking
Building a strong network can open doors to valuable career opportunities and help you stay on top of the latest developments in the industry.
7. Continuous learning
Follow experts on social media and participate in advanced training courses.
Top Cybersecurity Professional Certifications
They vary in level of difficulty and focus, here are some of the most notable ones:
1. CompTIA Security+
- Level: Beginner to intermediate.
- Description: A core certification covering a wide range of cybersecurity concepts, including network security, threats and vulnerabilities.
Risk management and security operations are an excellent starting point for beginners.
- Why it's important: Widely recognized and required for many entry-level security jobs.
2. Certified Ethical Hacker (CEH)
- Level: Intermediate to advanced.
- Description: This certificate focuses on ethical hacking and penetration testing techniques, and learns how to think like an attacker
To identify and protect vulnerabilities in systems.
- Why it's important: Very useful for those interested in penetration testing and security assessment.
3. Certified Information Systems Security Professional (CISSP)
- Level: Advanced.
- Description: It is one of the most prestigious certifications in the field of cybersecurity, covering eight key areas (Domains) of cybersecurity.
Requires a minimum of five years of practical experience in two or more of these areas.
- Why it's important: Required for leadership and management positions in cybersecurity and demonstrates a deep understanding of overarching security concepts.
4. Certified Information Security Manager (CISM)
- Level: Advanced.
- Description: Focuses on information security management, security program development, incident management, and risk management, targeting professionals who manage
or oversee information security programs.
- Why it's important: Ideal for professionals aspiring to management roles in cybersecurity.
5. Offensive Security Certified Professional (OSCP)
- Level: Advanced and very practical.
- Description: A hands-on certification that focuses entirely on practical penetration testing, requiring passing a difficult practical exam that involves penetrating multiple systems in a lab environment.
- Why it's important: It is the gold standard for penetration testing professionals and demonstrates strong practical skills.
6. Cloud Security Certifications
Cloud services (e.g. AWS Certified Security - Specialty, Azure Security Engineer Associate) are increasingly important.
Practical tips for everyoneWhat is your personal data
It is essential that you take steps to protect your personal data and sensitive information, here are some practical tips that you can apply in your daily life:
1. Use strong and unique passwords
- Length and complexity: Make your passwords long (at least 12 characters) and include a mix of upper and lowercase letters, numbers, and symbols.
- As well as uniqueness: Don't use the same password for more than one account, if one account is compromised, attackers won't be able to access your other accounts.
- Password Managers: Use password management apps to securely generate and store strong passwords.
2. Enable Multi-Factor Authentication (MFA)
MFA requires a second verification factor, such as a code sent to your phone, a fingerprint, or an authentication app, activate it on all your accounts that support it.
3. Be wary of phishing messages
- Source Verification: Always check the sender's email address or message link before clicking on any links or downloading attachments.
- Also, warning signs: Look for spelling errors, urgent and unexpected requests, or offers that seem too good to be true.
- Also, don't share sensitive information: Don't enter your personal or financial information into web pages you access via links in suspicious emails.
4. Update your programs and systems regularly
5. Use anti-virus and anti-malware programs
and remove any potential threats.
6. Back up your data regularly
7. Be careful when using public Wi-Fi networks
When using these networks, use a virtual private network (VPN) if you must use public Wi-Fi.
8. Monitor your bank and financial accounts
Science Club Academy is your gateway to cybersecurity excellence
and qualifying national talent to fill this gap, this is where Science Club Academy as a trusted partner in your educational and professional journey.
Why choose the Science Club Academy?
- Sophisticated and up-to-date curricula: Our training programs are designed in collaboration with industry experts to ensure they cover the latest technologies, threats, and best practices
At Cybersecurity, we ensure that you will learn the most in-demand skills in the market.
- As well as expert and certified trainers: Our trainers have years of practical experience in the field of cybersecurity and hold prestigious professional certifications, and will provide you with the theoretical knowledge and practical experience needed to succeed.
- There is also an interactive and hands-on learning environment: We emphasize project-based learning and hands-on labs, where you will have the opportunity to apply what you learn
In real-life scenarios, this approach ensures that you will gain practical skills that are immediately applicable in the work environment.
- Plus post-training support: Our relationship with you doesn't end once the course ends. We offer ongoing support, including career guidance, resume assistance, and connecting graduates with job opportunities in our extensive network of partners.
- Accredited certificates: Our programs are designed to qualify you for globally recognized professional certifications, enhancing your value in the job market.
- Moreover, a regional focus: We understand the cybersecurity requirements and regulations in Saudi Arabia and the UAE, and we adapt our curriculum to suit these needs.
This gives our graduates a competitive advantage in the local market.
- Whether you are a novice looking to enter the world of cybersecurity, or a professional who wants to develop your skills and specialize in a particular area.
Science Club Academy is the place for you. Join us today and start building your future in this dynamic field.

Future Trends in Cybersecurity 2026
It's important to take a look at the key trends that will shape cybersecurity in 2026 and beyond:
1. Artificial Intelligence and Machine Learning in Cybersecurity
to detect and respond to threats faster and more effectively, but also by attackers to develop more sophisticated and automated attacks.
This will create a constant arms race between defenders and attackers.
2. IoT Security
Many IoT devices lack basic security features, making them easy targets for attackers, and securing these devices will require innovative solutions and strict security metrics.
3. Quantum Cybersecurity
which focuses on developing Quantum-Resistant Cryptography algorithms to protect data in the age of quantum computing.
4. Threat-Driven Cybersecurity
Security is prioritized based on the most likely and impactful threats to the organization, which requires a deep understanding of the threat landscape
and the ability to predict potential attacks.
5. Cybersecurity as a Service - CSaaS
This will lead to the growth of Managed Security Service Providers (MSSPs) and advanced technologies without having to build costly in-house security teams.
6. Regulations and increased compliance
This will increase the importance of compliance with these regulations and will require organizations to invest in cybersecurity solutions that ensure compliance.
Critical for anyone who wants to succeed in this field.
As Saudi Arabia and the UAE undergo a rapid digital transformation, the Kingdom of Saudi Arabia and the United Arab Emirates (UAE)
The need for qualified competencies capable of protecting cyberspace and securing the digital future is growing.
You'll find everything you need to become a cybersecurity expert and make your mark in this ever-changing world.
Start your journey today towards a secure and prosperous future.


No comment